11th October: KSK Rollover time
On the 16th of September 2018 the ICANN board made the final decision to go forward with the Key-Signing-Key (KSK) Rollover in the root zone.
Most ISPs and other DNS operators prepared for this to happen last year (2017), but when some strange measurement results appeared, ICANN canceled the roll on short notice. Now, one year later, everything is set in motion again. Let's hope it isn't groundhog day!
If you can't remember or if you are new to the subject, we have collected the most important facts for you below.
What’s going on?
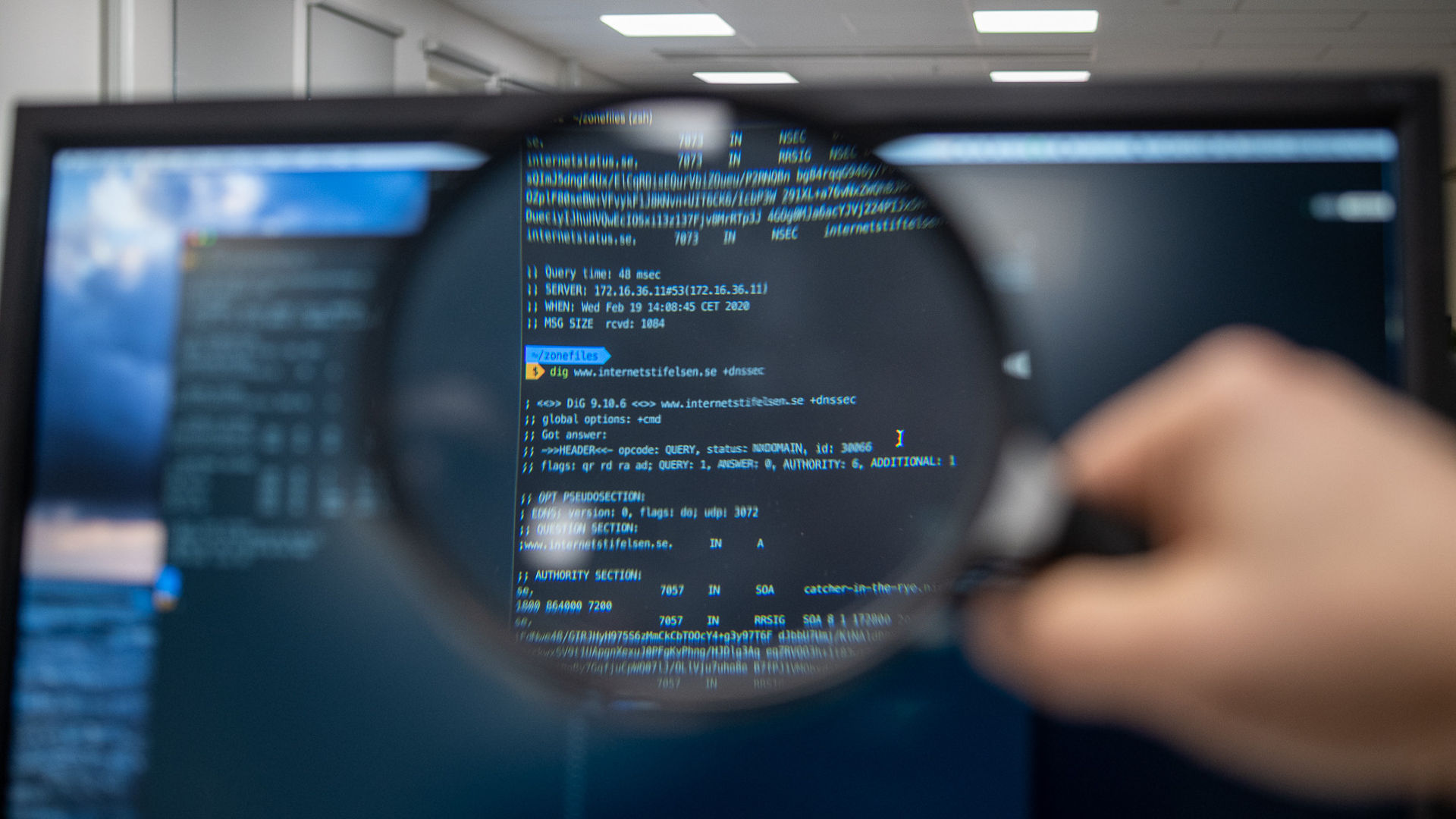
On October 11th, 2018, the Key Signing Key (KSK) used since 2010 to sign the root zone will be replaced. After this date, anyone who doesn’t have the new Key Signing Key (KSK) configured in their resolver (application/software used to resolve DNS queries) as a trust anchor won’t be able to reach resources on the internet signed with DNSSEC, since the authenticity of the query response won't be validated any longer.
Important dates
- July 11, 2017: Publication of new KSK-2017 in DNS root zone
- September 19, 2017: Size increases for DNSKEY response from root name servers
- October 11, 2018: New KSK-2017 starts to sign the root zone DNSKEY RR set (the actual key rollover event)
What do I need to do?
DNS service providers who have enabled DNSSEC validation should confirm that all their systems are updated with the new KSK as a trust anchor and verify the signature with the new KSK. This will happen automatically with most modern resolver software thanks to RFC5011. Updating the KSK is crucial for the validation of DNSSEC signatures, which is required in order for DNS resolvers continue to work properly after the key rollover. Without the correct root zone key (KSK) DNSSEC validation will cease to work and DNS resolvers won’t be able to answer any DNS queries for signed domains.
This means that if you have support for RFC5011, as for example in modern versions of Unbound or BIND, it is enough to verify that the new key is in place sometime during the second half of August. If it is not there by then, you will need manual intervention.
What are the consequences of not replacing the key?
DNSSEC validation will stop working for resolvers that has validation enabled but do not have the new KSK configured as a trust anchor.
What do I need to do if the automatic key rollover didn’t work?
It depends on what kind of software you are using in your resolvers. Either the key rollover takes place automatically or it will need manual intervention. To find out how it is in your case, please contact your software supplier.
Here is where you find more information!
Questions?
Contact registry@internetstiftelsen.se