It is time for yearly clean-up of your domain!
It is more common to have routines for adding new functions than for cleaning-up old ones that are not in use anymore. Time for clean-up!
It is more common to have routines for adding new functions than for cleaning-up old ones that are not in use anymore. Time for clean-up!
The material presented in this article is taken from Thomas Ido's thesis "Mapping the DNSSEC Quality of DNSSEC Secured .se Domains"
It is now possible to apply for a university course in DNS provided by The Swedish Internet Foundation at KTH Royal Institute of Technology. The course provides basic and detailed knowledge of DNS and DNS protocols, including DNSSEC and IDN. The course is aimed at professionals.
Moritz Müller is a research engineer at SIDN, the registry of the Dutch country code top-level domain. But for three months he is working in Stockholm at The Swedish Internet Foundation, which was made possible through a close collaboration within the CENTR community.
Internetstiftelsen and Netnod joint forces in order to outline some of the critical elements you should look for when setting up or procuring a DNS service for an enterprise .
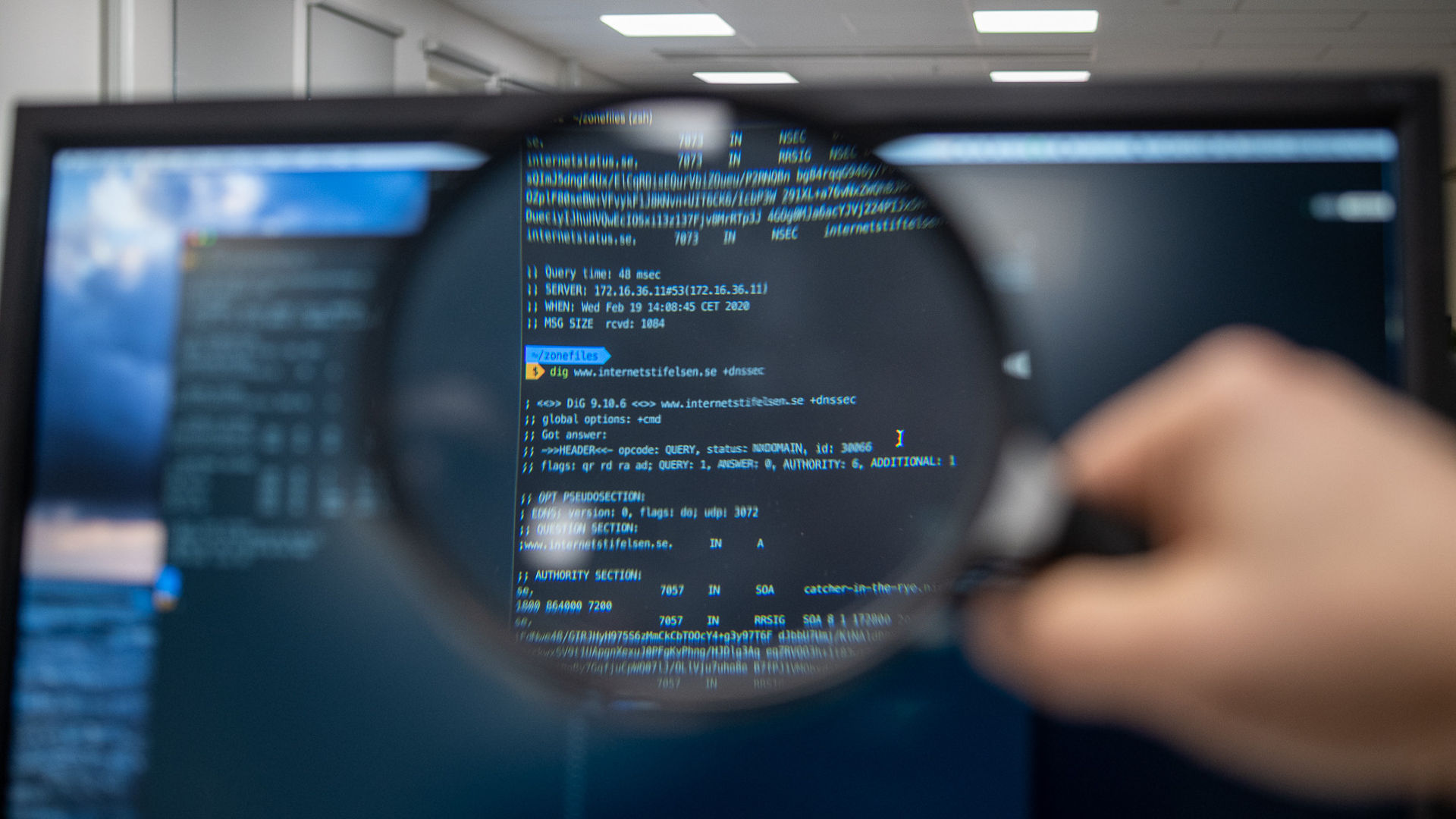
The Swedish Internet Foundation has been a big supporter of DNSSEC from the beginning. .SE was the first TLD to be DNSSEC signed back in 2005, long before the root. Now we continue to innovate and allow DNS operators to update registry data with the help of DNSSEC.
DNSSEC is currently enabled for almost half of the .se zone, and slightly less than that for .nu. To reach the other half of the “market”, DNSSEC needs to be more accessible. That is why we now add a new and easier method of updating records.
The Swedish Internet Foundation and DNS-Labs will provide a Postgraduate Research scholarship at Karlstad University to research DNS. This initiative is an unique opportunity to collaborate with one of the leading scientific and educational institutions in Sweden.
The Swedish Internet Foundation has for the last couple of months been working together with Shumon Huque of Salesforce, and the Internet pioneer Steve Crocker. Together they are solving the problem with multi-signer DNSSEC.
The third round of the class covering the internet’s domain name system, DNS, at the Royal Institute of Technology, KTH, started in January 2021. The class is a cooperation between KTH and the Swedish Internet Foundation.
ns.se (former DNS Reference Group) is our forum where you can share knowledge and discuss questions about DNS. Join by signing up for the mailing list here.
